Configuring settings
Before the Active Directory binding can be activated to import users and groups from the Active Directory to octoplant, certain settings need to be configured in the AdminClient.
In order to configure the settings for the Active directory binding, proceed as follows:
- In the Synchronisation tab, select the Activate button.
- In the tab Authorisation, you have to choice to select between Authorisation by operating system and Authorisation by operating system and access management. Afterwards, click on Ok. (For more information on these settings, please refer to AdminClient ->Account policies).
-
In the ribbon, click on the option Configure.The dialog Active directory binding will then be displayed.
-

-
Implement the necessary settingsMandatory fields are marked with a red star *.
- Click on OK.The settings are now saved and the dialog will close.
Note
When configuring the Active directory connection, data supplied by the IT department, for example, is often copied from an email or a Word document. It can happen that characters are changed or added by the corresponding word processing program. This will be indicated by an error message. To prevent this, we recommend entering the data manually.
Server
| Element | Description | Example |
|---|---|---|
| Address | Name, IP address or domain of the Active Directory servers!!! note If the computer from which you want to connect is not included in the domain of the Active Directory server, a connection will only be possible via the name or IP address of the Active Directory server | 10.0.201. |
| Port | Active directory server portInteger values ranging from 0 to 65535 are possibleThe default port for encrypted connection is port 636 (default port for unencrypted connection is 389)If a port is already being used for something else, select another one | 63 |
| SSL encrypted | Encrypted or unencrypted connection to the Active Directory server.By default, the connection to Active Directory is made using the LDAP protocol. If the SSL Encrypted checkbox is selected, the LDAPS protocol will be used | þ SSL encrypte |
| User name | User name for access to the Active Directory ServerFormat:<User name>or<Domain>`or@<domain> |
octoplant |
| Password | User name for access to the Active Directory Servermasked displa | •••••••• |
| DC | DNS name of the domainInformation according to the Active Directory format The parts of a domain name separated by dots are divided into individual sections in the Active directory. Each section is intiated by the prefix DC (= Domain Component). The individual sections are separated from each other by commasie domain “vdns.tst.dom” is mapped as follows: DC=vdns, DC=tst, DC=do | DC=vdns, DC=tst, DC=do |
| DN “All Users” | Distinguished Name (= DN) of the Active Directory group, within which users (and other groups), that are to be imported, are searched for.Entries corresponding to the Active Directory Format. A distinguished name represents an object in a hierarchical directory. The distinguished name is written from the lower to the higher hierarchy levels. The object itself is introduced by the prefix CN (= Common Name). The individual parts are separated from each other by commasFor the group “Club27” in the folder “Usersâ€, the Distinguished Name looks like this: CN=Club27, CN=User | CN=Club27, CN=User |
| DN “Administrators†| Distinguished Name (= DN) of the Active Directory group, whose users are to be imported into the Administrators groupEntries corresponding to the Active Directory Format. A distinguished name represents an object in a hierarchical directory. The distinguished name is written from the lower to the higher hierarchy levels. The object itself is introduced by the prefix CN (= Common Name). The individual parts are separated from each other by commasFor the group “Reservoir-Dogs” in the folder “Usersâ€, the Distinguished Name looks like this: CN=Reservoir-Dogs, CN=Users | CN=Reservoir-Dogs, CN=Users, OU=SecurityGroup |
Path specification:
Paths need to be entered in full in the Active Directory Binding dialog. If the path contains special characters, such as “+” (for example, OU=W+D), this special character must be provided with an escape sequence “” (for example, CN=Reservoir-Dogs, OU=W+D).
You can use the Check button to test whether the server details are correct.
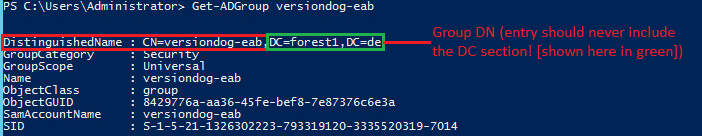
Issuing Distinguished Name of Active Directory Group
In the fields DN “All Users†and DN “Administrators” the distinguished name of an Active Directory group is specified. The distinguished name can be issued via the PowerShell command`Get-ADGroup
Example:
SSL encrypted connection to Active Directory server fails with the following error message. How can I resolve this problem?
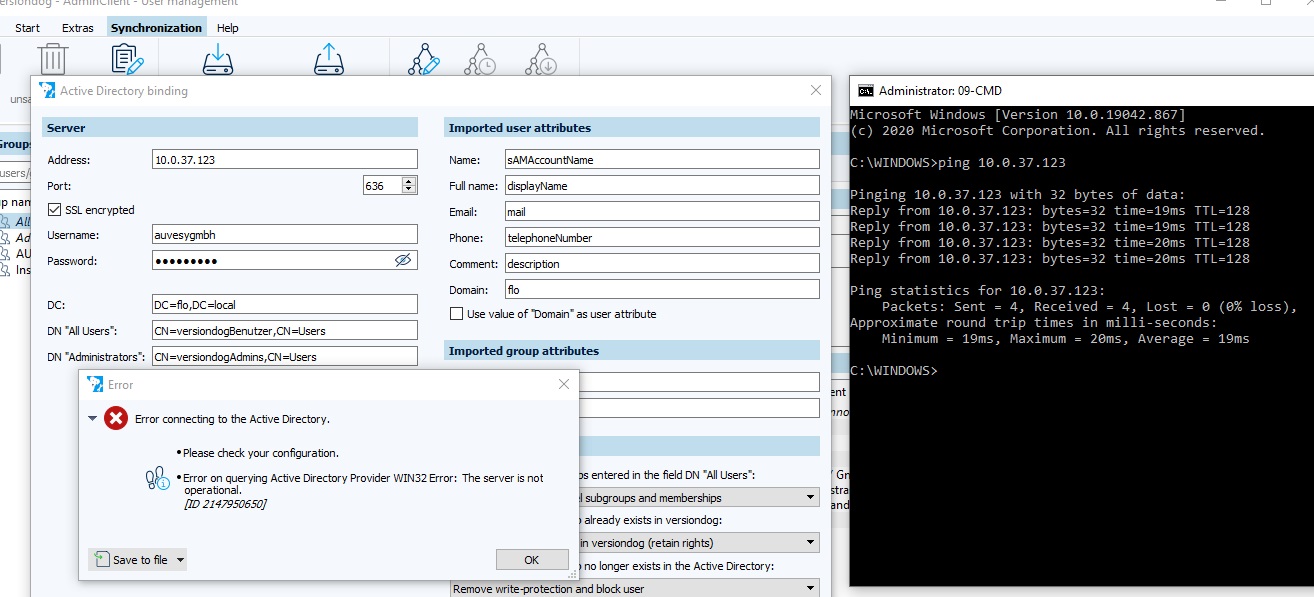
Check if the name in the certificate matches the name in the request.
In the above example, the IP address was used instead of the computer name “FS-2019” during configuration. Since only the name “FS-2019” is stored in the certificate, the displayed error occurs.
To fix the error, specify the computer name “FS-2019” in the Address field.
Imported user attributes
| Element | Description | Example |
|---|---|---|
| Name | Attribute from the Active Directory, which is used as user name in octoplantDuring the import, the name of a user is set according to the value of the attribute from the Active Directory | sAMAccountNam |
| Full name | Attribute from the Active Directory, which is used as the full name in octoplantDuring the import, the name of a user is set according to the value of the attribute from the Active Director | displayNam |
| Attribute from the Active Directory, which is used as the email address in octoplant.During the import, the email address of a user is set according to the value of the attribute from the Active Directory | mai | |
| Telephone | Attribute from the Active Directory, which is used as the telephone number in octoplantDuring the import, the telephone number of a user is set according to the value of the attribute from the Active Directory | telephoneNumbe |
| Comment | Attribute from the Active Directory, which is used as a comment in octoplantDuring the import, the comment of a user is set according to the value of the attribute from the Active Directory | descriptio |
| Domain | Domain name or user attribute from the Active DirectoryIf the checkbox Use value of “Domain” as user attribute has been cleared, the NetBIOS name of the domain will be entered. This is the default setting.If the checkbox Use value of “Domain” as user attribute has been selected, any user attribute can be specified from which the domain name can be read or used.2 Special features: For the userPrincipalName and distinguishedName attributes, the first sub-domain or domain found is used as the domain name in each case.Examples:distinguishedName:CN=UserName, OU=Development, OU=UserAccounts,OU=Organisation, OU=Company, DC=subDomain,DC=Domain, DC=localHere the value of the first “DC=” is used as domain name, therefore”subDomain”. userPrincipalName:user@subdomain.domain.local |
Imported group attributes
| Element | Description | Example |
|---|---|---|
| Name: | Attribute from the Active Directory, which is used as user name in octoplantDuring the import, the name of a group is set according to the value of the attribute from the Active Directory | c |
| Comment: | Attribute from the Active Directory, which is used as group comment octoplantDuring the import, the comment of a group is set according to the value of the attribute from the Active Directory | descriptio |
Import options
| Element | Description |
|---|---|
| Procedure for the groups entered in the DN “All Users” field | Import users (do not import groups or memberships)Only users are imported from the AD. Groups and memberships are not imported Import users and groups and membershipsThe groups specified by users (these must be groups and not OUs) are imported into octoplant. (Users are assigned to their respective groups). |
can be found fast and easily with a tool for managing the Active Directory. For example, the Active Directory Explorer from Microsoft is such a tool. If the port is explicitly specified, the SSL connection can also be checked.
Example:
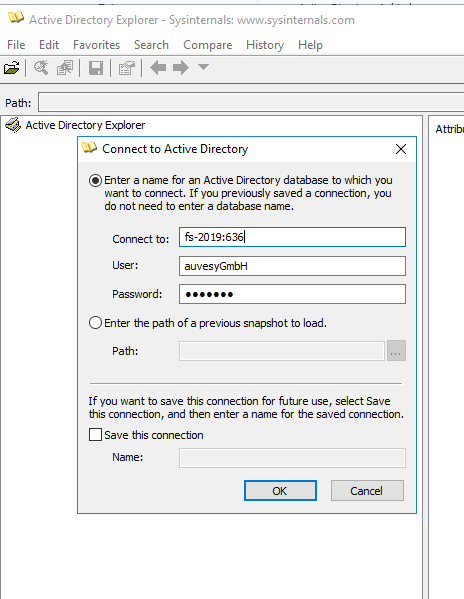
The following screenshot shows the information needed to configure the Active Directory Binding so as to be able to import the group “Club27” from the “Users” folder via Active Directory Explorer. Information relevant to each other can be recognized by the same number.
How can I import a certificate on theoctoplantserver or check its availability?
A root certificate identifies a certification authority (CA). With this root certificate, a CA signs one or more subordinate certificates that sign the SSL certificates of the end users.
The root certificate must be imported to the server. To do this, double-click the exported certificate and file it under Trusted root certification authorities.
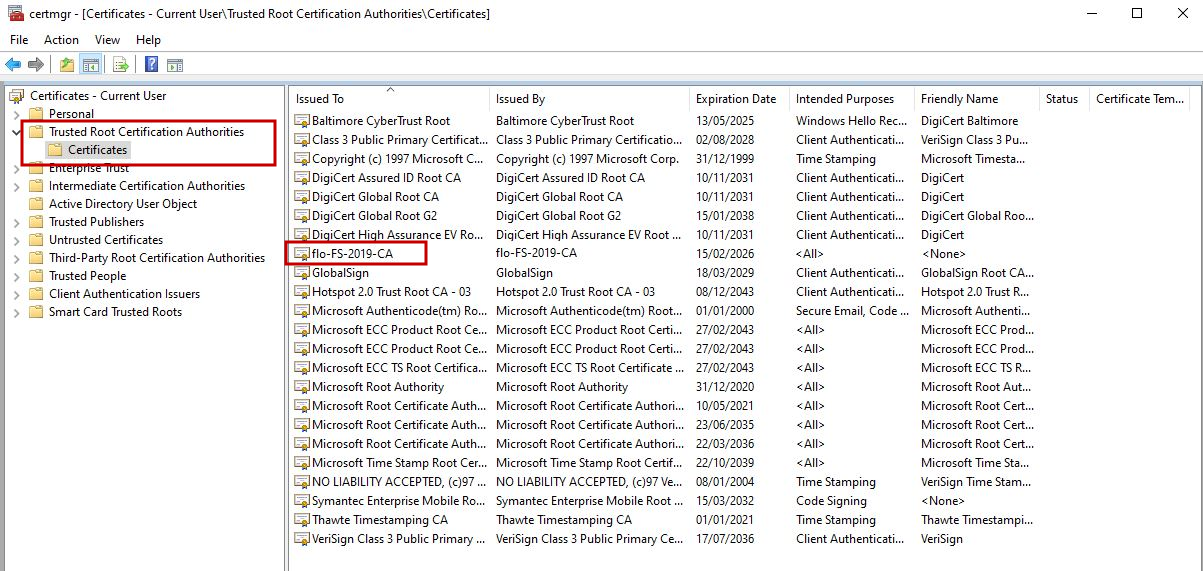
To display the certificate, press Win + R and enter certmgr.msc (or certlm.msc) in the Run dialog.